Your Account
The standard environment initially given to users includes tcsh as the command shell, and a standard setup for graphical interfaces on the Linux workstations. Experienced users can change or customize these environments to suit their preferences using the information here.
- Login With Your Campus Account
-
Eligibility: You must either be an ECE graduate or undergraduate student, or currently be enrolled in (or on the waitlist for) an ECE supported class. The computers that are available for general use are in Kemper 2107.
If you DO NOT have a UCD computer account -- Please call IT-Express at 530-754-HELP.
If you DO have a UCD computer account:
♦ Sit in front of one of the displays in Kemper 2107 and move the mouse to activate the display.
♦ At the login prompt, type in your campus username.
♦ At the password prompt, enter your campus passphrase.
♦ DO NOT use the numeric keypad (on the right side of the keyboard) while typing; instead, use the number keys just above the letter keys. Also, you may not see anything in the password field while typing.If you have questions or problems with your account, email [email protected].
- tcsh and System Startup Files
-
Tcsh, an extended version of csh, is the default command shell used on all ECE computers. tcsh allows us to maintain a system-wide standard environment. These system files are stored in the directory, /etc, and are called csh.cshrc, csh.login, and csh.logout. These files are processed before any corresponding local versions of .cshrc, .login, and .logout.
To bypass processing of one of the system dot files and execute only your local file create an empty file called .NONSTANDARD.cshrc, .NONSTANDARD.login, or .NONSTANDARD.logout in your home directory. The simplest way to create an empty file is by using the touch command. i.e. touch ~/.NONSTANDARD.cshrc
To bypass all system dot files create a file called .NONSTANDARD
A user’s .cshrc should not define path and environment variables that are for software packages supported on the ECE system. Instead, enter the software package in .software by running the appropriate setup scripts. The soft system is bypassed when any one of the .NONSTANDARD files exist.
- Erase Characters and Other Keyword Mappings
-
One point of confusion that often occurs involves the mapping of the delete or backspace key to properly erase characters.
To identify your current settings, type:
stty -a
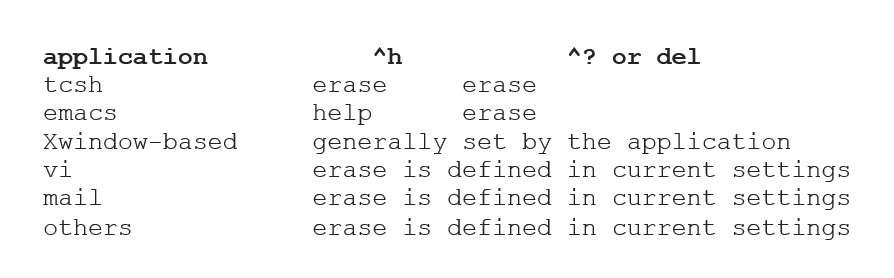
Then look for "erase =". Common settings include ^h, ^?, or del. (del and ^? have the same function). Most applications use the current settings to perform line editing functions, such as erase. Some applications have a default definition for ^h and ^?. The following table describes these conventions:
To identify how a key is mapped on your keyboard, you can type: ‘ctrl-v’ followed by any key. Its mapping is echoed to your display. To identify the locations of ^h on your keyboard, check out the following
To change the current setting of the erase character, type: stty erase ctrl-v KEY where KEY is the key that you want to use to erase characters.
- Disk Quotas
-
Disk quotas represent the amount of disk space that you are allocated for your ECE home directory. The standard disk quota for students is 1GB.
Checking Your Disk Quota
Login to a Unix/Linux machine, either locally or remotely using a program such as SSH. Enter the command “quota -v” at the prompt. The output will look something like this:

Finding and Removing Expendable Files
Use the “du” command as shown below to obtain a report of the number of kilobytes used in each directory of your account:
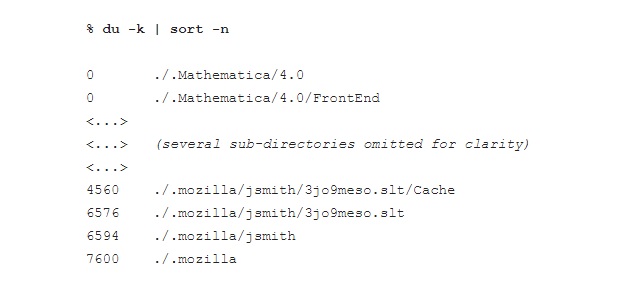
Note that the results are sorted in ascending order of disk usage. This example shows 4560KB in ./.mozilla/jsmith/3jo9meso.slt/Cache and that accounts for most of the 7600KB usage under ./.mozillaUse the standard Unix commands for working with directories and files to navigate directories and delete any large expendable files. Prime candidates for removal are:
♦ “core” files. These huge program dumps are useless to most people
♦ files in Cache directories
♦ compiled programs and .o files that you can recompile later if needed. - ECE Printers
- Print quotas are not used in ECE instructional computing labs.
♦ Undergraduate Instructional Lab Kemper 2107 -- Canon ImageRunner 4025/Black and White/Spooled by https://campusprinting.ucdavis.edu
♦ Undergraduate Instructional Lab Kemper 2110 -- Canon ImageRunner 4225/Black and White/Spooled by https://campusprinting.ucdavis.edu
♦ Graduate Study Room Kemper 1107 - Identifying or Modifying Your File Execution Path
- The basic execution path is:
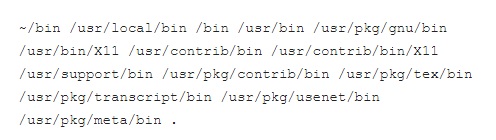
This execution path gives you access to basic utilities and the most popular software packages. However, it may not give you access to the packages that you need to run. Beginning Fall 95, we have implemented a new way of setting up your execution path using the script, Soft.
What is soft?
Soft is a system for generating path and other shell variables based on user selected software packages. The soft system generates only those paths and variables that are required, which is important due to the large number of packages available on the ECE system. Specifying all paths would lead to “ridiculously long path” shell error messages. Furthermore, soft facilitates system maintenance by organizing packages according to architecture/operating system.How do I add a package to my execution path?
To add a package, run the command, setup, followed by an argument that describes the package that you want to add.How do I know which packages I have added to my path?
The set of software packages selected by the user is kept in a file called .software under his home directory. Generally, a user should not edit .software directly.How does soft work?
On the start of a new shell, soft consults the appropriate database and generates the paths and shell variables needed for each package in .software. The result is a shell script that is then source’d (read in) by the shell. Because an ECE account may span multiple machine architectures and operating systems, the script generated by soft is architecture/operating system specifc. For example, on a HP workstation running version 9.05 of the HP-UX operating system, the script is called .software-cache.csh.HP-UX_A.09. On a DEC 3000 300/AXP running OSF/1 version 3.2, it is called .software-cache.csh.OSF1_V3. Soft generates a new script only when the .software file or the database has changed since the last time soft has run. If there are no changes, the old script is source’d, saving computer time. You will also notice these file names in your account after running setup.How do I remove a path that I have added via the setup command?
To remove a path, type unsetup and the argument that describes the pathPaths not supported by soft can be defined in .cshrc by statements of this form:
set path = (<directory list>)
Where <directory list> is a space-separated list of directories. You can include the existing path by using $path as one of the elements in the list, e.g.:
set path = (new_dir $path)
Be aware that if $path is included in the list it will double in size every time .cshrc is processed. Normally, all the paths a user will need are supported by soft, making definitions in .cshrc unnecessary. - File Security
-
Default Permissions
The standard setting from the system cshrc file is ‘umask 066’, meaning the owner of the file has full privileges, and other people may traverse your directories but not read them or the files contained within them. Moreover, the permissions on home directories created after September 1997 will only allow read and write to the owner. If you wish to increase the security on your files to match the current policy, please typechmod -R go-r ~
Users who wish to have the old behavior should, add the follow line to the top of their .cshrc file.umask 022
and type the following linechmod a+r ~
Be warned, this will allow any user to read files.To give access to a file or directory to others for the purposes of sharing files or making a web page, type
chmod a+r <filename or directory>
File transfers should be through the /tmp directory, so do not make directories or files under your home directory writable to others. Users who are working on group projects that need to share files frequently should email [email protected] for further instructions.Do not under any circumstances give write access to your home directory as this will allow any user to impersonate you and read your files! They may login without a password to your account and do anything they want, including reading mail, erasing files, and forging mail.
Additional Security
Although the current umask will not allow reading of files, there are circumstances in which a file is created with less security. In those cases, it may be possible for another user to read that file because our default umask still allows for directories to be traversed. In these cases it may be desirable to have your directories non-traversable so that files can not be access even if they have read permission.If you have sensitive files in your account, you can change the default setting to eliminate access by anyone else by adding the line,
umask 077
to your .cshrc file. To increase the security on an individual file, typechmod go-rwx <filename or directory>
- File Management: Storage, Backup and Recovery
-
File Storage Quota
Current, active files should be stored in your home directory. Undergraduate and Graduate students have a quota of 1GB. To monitor the disk space usage in your account, run the command “quota -v”. The system will respond with your usage and quota in units of 1024 byte blocks.Temporary File Storage Space
Each computer also has a space for temporary file storage in a directory called ‘/tmp’. If you need temporary storage space, you may write to ‘/tmp’. This space is not backed up; files more than seven days old are deleted, and files may be deleted even sooner if as needed. This space is especially handy for large files that you cannot write to your account (if you have exceeded your disk space allotment).Archival File Storage Space
If you have large files that you would like to archive, ie you need to have occasional access to them, but won’t be changing them often, and you are working at your disk quota, send an email message to ‘ece-support’.File Backup and Recovery
ECE file servers are backed up daily. To recover a file, send an email to [email protected]. Include the computer, path, filename, and range of acceptable recovery dates. - File Access (Home Directory, AMD and Path Names, Non-Home File Access)
-
How files are accessed, including files in your home directory as well as files on other ECE computers:
Home Directory Location
Your ECE home directory is accessible from any department Unix or Linux host as /home/username.Requests for custom disk space allocation arrangements on research lab hosts should be directed to the research lab manager or computing support.
AUTOFS and Path Names
AUTOFS, a public domain auto-mount daemon, will mount a file system from a remote machine on the local machine, allowing transparent access of the remote files. With the automounter in place, file systems are not mounted until you request that they be accessed. The files are actually accessed through symbolic links maintained by AUTOFS to avoid hanging when the host system containing the files becomes unavailable. For this reason the path name reflected by the pwd command may not be the same as the path you used to access the files. In spite of this, do not, under any circumstances, use the actual path name i.e. /.net1/boa/…. or /.homes/boa/…Non-Home File Access
If you want to access system files on a department computer or a publicly exported file system on another computer, ‘cd’ to entire export tree on reference. Upon receiving a request, such as ‘cd /net/boa’, AUTOFS will automatically mount boa’s entire file hierarchy. - Remotely Accessing Your Account
-
The .ece.ucdavis.edu Subdomain
The ECE computers are part of the subdomain, .ece.ucdavis.edu. Within the ECE department, you can refer to computers by the first part of their name. The name and IP address of each system is printed on the machine. However, if you are contacting snake from the campus domain (ucdavis.edu), you must refer to snake as ‘snake.ece’. From a domain other than ucdavis.edu, or ‘snake.ece.ucdavis.edu’.Logging On to Another ECE Host Using SSH
Once you are logged on to an ECE computer, you can begin a session with another ECE computer using the command ssh. For example, to begin a session on asp after logging onto another computer, type: ‘ssh asp’. Note that this method will allow you to change the host within the window where you typed the command. For further information, type: ‘man ssh’.Opening Another Xwindow
To bring up another xwindow on the local host, point the cursor to the root or background window and press the rightmost button; select the remote host name. When a window frame appears, press any button to bring up the window. Alternatively, click on the terminal in the bottom grey icon row. To initiate a log on to another ECE computer and configure for X window usage, use ssh with the -X option. For instance, ‘ssh -X asp’. You can then run X applications remotely by opening them via the command line.Connecting to a Machine with a Low Load Average
The best machine to connect to remotely is the one with the lowest load average. We have a program that automatically connects you with such a machine.
To connect to a machine in Kemper 2107, type 'snake.ece'.

